Rise of Best wireless CCTV camera system
How far are you familiar with the potential risks of a wireless CCTV camera system? With time, the technology has improved significantly in years, like an increase in the number of wireless and much more.
Due to its mere installation process and convenient viewing options, wireless security has become relatively famous.
Recently, a few months back, the Canterbury Bankstown mayor took a great initiative. Setting a few cameras on school perimeters to capture children’s drop-off and pick-up places.

1. What is a Wireless CCTV Camera System
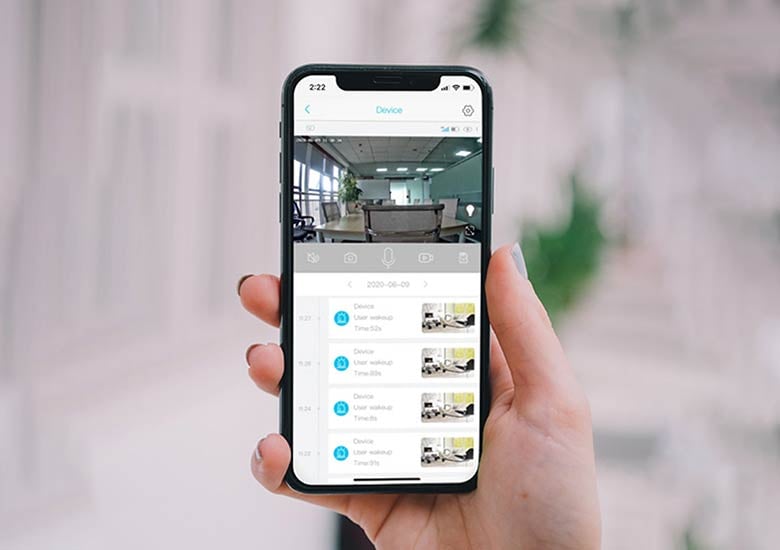
Wireless CCTV Camera System are closed-circuit television (CCTV) cameras that transmit a video and audio signal to a wireless receiver through a radio band. Many wireless security cameras require at least one cable or wire for power; “wireless” refers to the transmission of video/audio.
Wireless CCTV Camera System work by transmitting the camera’s video through a radio (RF) transmitter. The receiver connects to a built-in storage device or cloud storage, which gives you an easy link to access your images or video clips.
2. COVID-19 Risks
COVID-19 remains above our head action is taken with respect to avoiding the crowd hurdling. Near the school’s drop-off place.
The principal claimed that if the parents exceed the limit of 2 min parking, then the AI will capture the most common offenses.

3. wireless CCTV camera system for Home and the Risks
Apart from this, while you move down the streets, you may encounter with dozens or even more than hundreds of cameras hidden.
The best thing about wireless CCTV system for home use is that they rely on the internet to transmit data to different devices. However, it becomes quite simple for any hacker to find ways to tap into the footage and use it for iniquitous behavior.
There are Best Wireless CCTV System for Home but unfortunately does not come with encryption features.
It may sound unsatisfying, but the way CCTV cameras are developing with its technology brings potential threats that usually have wireless network faces.
Acknowledge the major threats, which can possess by any wireless device or wireless CCTV camera systems in specific.
4. Rogue access point setup
Generally, a rogue access point (AP) is a wireless mechanism. Installed in every network without any valid authorization from the network administrator. The whole motive of this fraud is to ruin the organization for his/s her intentions.
Trick the business and make them believe that their connectivity is legitimate AP. However, in reality, they are successfully falling under the trap. Made by an unethical hacker who can expropriate sensitive data from the business.
5. Duplicating or twinning the access point
Users don’t know rogue access points. Although, this can comfortably trick nearby CCTV cameras.
Connected with WIFI to come in contact because it can’t differentiate between legitimate and rogue AP. When it comes to creating an evil twin AP for malicious purposes, then it’s not challenging.
Though, with the help of Ka Metasploit, creating an AP has become a piece of cake. The software allows you to create fake Apps, gathers data, capture passwords, and browser attacks against clients.

6. Forbidden or Lost WIFI device threats
Most people are not much aware of these threats when it comes to wireless CCTV camera system security. In some cases, you may have locked your business WIFI surveillance with the most powerful security system.
But what if you lose the device that you used to log onto the very same network? The devices could be of anything like your smartphone or laptop.
But whoever recovers the device might have the capability to access your network based on saved or cloud data on your device.
Although the problem is common, taking the situation lightly at any possible costs, would result in a serious trap.
7. Issues with Configuration
When you are facing some issues with configuration, you may end up your surveillance system more vulnerable. Such problems occur where an individual tries to manage the APs by himself.
8. Unknown WPS threat Vector
wireless CCTV camera systems are protected with WPS or WIFI. It also helps to protect the router from any threats with the entry of a pin.
WPS security brings out several loopholes that effortlessly exploited by crooks. The problem discovered several years ago. It is patched in the best possible manner.
Every wireless security user must pay attention to the overall security of wireless networks. The irony of wireless security cameras is that they may result in additional security risks to your home and business.
But only if you take your time to understand what are you fetching up. Prioritizing cybersecurity a priority, you can get rid of most of the issues.
The main goal for cybersecurity is to make cameras more secure either through end-user behavior or technological advancement.